Article Contents
Nmap, which stands for “Network Mapper,” is a well-known open-source network scanner that is used by both professional network administrators and “good hackers.” It can do more than just scan networks; it’s also a useful tool for keeping track of network inventory, planning service upgrades, and making sure servers and services are always online. It’s helpful to learn about Nmap’s history in order to fully understand how important it is.
Gordon Lyon, a security expert, first wrote about Nmap in an article for Phrack in September 1997. Phrack is an online magazine that is mostly written by and for hackers. Nmap has changed a lot over the years. It was first made using a mix of programming languages, such as C, C++, Python, and Lua. Nmap started out as a tool for Linux users, but it now works with Windows, Mac OS X, Gentoo, and a number of BSD operating systems as well. Notably, Linux fans are still the main people who use this tool.
One thing that sets Nmap apart is that its website has a classic look that hasn’t changed much over the years. While this may seem a bit out of date in today’s world, the website still works and is full of detailed information about the product that is available in many languages. This further solidifies Nmap’s reputation as a reliable and important tool for network management and security.
NMAP Specification
Nmap is a strong and flexible program that can do many things, like finding networks, scanning ports, finding hidden systems, and checking for security holes. The tool is free and open source, and it can be used on many devices.
| Feature | Description |
|---|---|
| Port scanning | Nmap can scan ports to identify open ports and the services running on them. It can also detect closed ports, filtered ports, and ports that are in an unfiltered state. |
| Host discovery | Nmap can discover hosts on a network, even if they are not responding to ping requests. |
| Operating system detection | Nmap can detect the operating system running on a host by analyzing its TCP/IP stack and other characteristics. |
| Version detection | Nmap can detect the versions of the services running on a host. |
| Scripting | Nmap supports scripting, which allows users to automate tasks such as vulnerability scanning and fingerprinting. |
| Stealth scanning | Nmap can scan ports in a stealthy manner, which makes it more difficult for the target host to detect the scan. |
| Parallel scanning | Nmap can scan multiple hosts and ports in parallel, which can significantly improve the speed of the scan. |
| Output customization | Nmap provides a variety of options for customizing the output of its scans, including XML, JSON, and Grep-able output. |
| Visit Website |
What is Nmap?
You can learn more about Nmap here. It is a free and open source tool for finding networks and making sure they are safe. It’s also used by many system and network managers to keep track of when services will be upgraded, make an inventory of the network, and see how long hosts or services are up.
Nmap looks at raw IP packets in new ways to find out what hosts are on the network, what services they give, what operating systems they run, what kinds of packet filters and firewalls are in use, and a lot more. It was made to quickly look through big networks, but it works fine on single sites too. No matter what kind of computer you have, you can run Nmap.
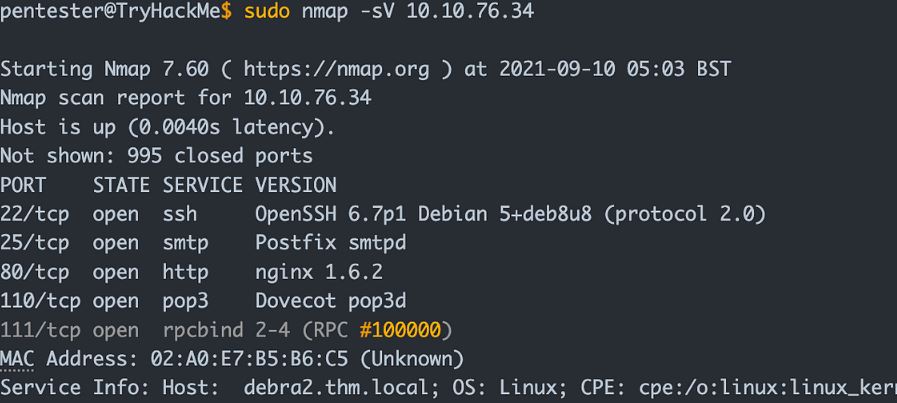
NMAP review: Features
You can use the “nmap” command on a range of IP addresses or a single address, and it will return basic information about devices that are online, open ports, and network connections between devices. In Zenmap, this information can be shown as a graph. The media access control (MAC) addresses will also be recorded by Nmap. The manufacturers are included in the MAC address, which can help you find printers, routers, or even video game consoles that are connected to the network. But for endpoints and servers, the MAC address will usually only give you the name of the company that made the network card.
To get more information, you will need to use other commands. Nmap has learned how to change the data packets that are sent across the network in order to gather information about the network. These features let users intercept (also called “packet capture”), filter, reroute, or send data packets that have been changed in some way.
Most packet manipulation can be done with built-in commands or scripts, but the Nping tool stands out. Nmap can do port analysis and get detailed information about the hosts it scans by sending packets that have been changed. The type of host or device, the services that are running on the ports, the operating systems, and the level of confidence in the analysis are all shown by scans. With deeper scans, the analysis can give information about the host’s versions, patch levels, and expected uptimes.
NMAP review: Ease of use
A powerful and all-around tool called Nmap is used to map networks and scan ports. But it can be hard to use at first, especially for new users. The syntax of Nmap’s command line is one of the hardest things about using it. Each of Nmap’s many options and features can be used by giving it a certain command. For new users, this can be too much, and it may take some time to figure out how to use Nmap well.
The output of Nmap is another problem that needs to be solved. Nmap can give you a lot of information, and it might be hard to figure out what it all means. This is very important for scans that are complicated. The good news is that Nmap is a strong program that can help people who need to map and scan networks, like network administrators and security experts. The Nmap documentation, tutorials, and online forums are just a few of the places where people can go to learn how to use Nmap.
NMAP review: Customer support
Because Nmap is a free and open-source software application, it does not offer the conventional forms of customer support. For example, there is no customer service phone number or online support ticket system. On the other hand, there is a sizable and bustling community of Nmap users and developers who are always ready to assist with any questions or issues that may arise.
The Nmap mailing list is the most helpful resource for obtaining support for Nmap. The Nmap mailing list is a forum with a high volume of users where developers and users can discuss issues, ask questions, and share hints with one another. Because the mailing list is monitored by the developer of Nmap, Fyodor, as well as other experienced Nmap users, you can be certain that you will receive a response that is helpful.
Final Words
Nmap is a flexible tool for exploring, managing, and checking the security of networks. It has features like finding hosts, scanning ports, finding versions, figuring out what operating system is running, and evaluating vulnerabilities. Nmap is flexible and adaptable because it has a command-line interface and a lot of scripting features. The people who use it are always adding new modules and plugins.
It has some big problems, like the chance of interrupting the network, not being compatible with other systems, and being found by intrusion detection systems, but it is still a useful tool for network administrators and security experts.
The Good and Bad
Nmap can find out what operating system is running on a host by doing things like “fingerprinting” the host’s TCP/IP stack and looking at how it responds to different probes.
The Good
- Powerful network scanning capabilities.
- Extensive customization through scripting.
- Supports multiple output formats.
- Cross-platform compatibility.
The Bad
- Can be complex for beginners.
- May raise security concerns if used improperly.
- Some features may require advanced knowledge.
Answers answers
Nmap is a powerful tool that can be used by white hat hackers who want to scan and analyze the traffic and logs on a network. It is possible for it to assist you in discovering hosts, ports, services, vulnerabilities, and other information about the network that you are looking to penetrate. However, just like any other tool, it has both its benefits and drawbacks.
Executes a dictionary-based attack on the user’s password using HTTP form-based authentication. For the purpose of performing password guessing, this script makes use of the unpwdb and brute libraries. Using the creds library, any guesses that are correct are added to the nmap registry, where they are available for use by other scripts.
